10 Must-have Active Directory Tools
Written by Clifford
Here we list 10 tools for the AD administrator to make AD tasks easier and to ensure compliance with audit requirements. The list covers the whole spectrum of adding data via LDAP, provisioning users, managing forests and domains, querying data, and complying with audit requirements.
All of these products require that you buy them unless otherwise noted.
Softerra LDAP Administrator
Active Directory has an LDAP interface. This means those who are comfortable using the LDAP commands ldapmodify and ldapsearch to add and query data might already be using Active Directory in that way.
Softerra’s LDAP Administrator makes this easier, because it gets rid of the need to know how to spell the schema attribute when working with LDIFs. You can enter Person, InetOrgPerson, or other objects, and it gives you a screen with all the attributes for those object types. So then you just type in the values.
Softerra Adaxes

Softerra also makes Adaxes. This assists with user provisioning and automates some of the workflow approval processes. Plus, it provides a web interface for administrators and self-service.
Adaxes lets you run queries across different AD domains even if they are in different forests. It also has a template to facilitate mass updates. For example, you can write “%firstname% %lastname% “to update the %name% property for however many records you have selected.
Anturis Active Directory Monitor
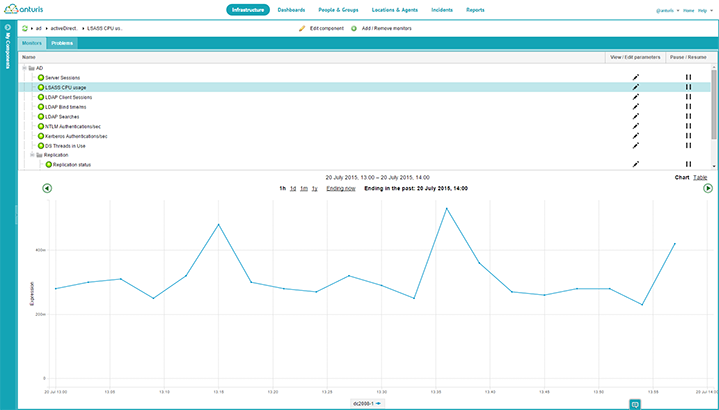
Anturis offers a fully cloud-based monitoring application that allows you to keep abreast of your Active Directory infrastructure on a constant basis. Active Directory monitoring is but one facet of this complete cloud based IT stack monitoring system that allows you to keep abreast of multiple elements on a single dashboard that you can access from anywhere through any web browser.
Manage Engine AD Query
AD Query uses the familiar LDAP Polish notation, i.e. the operator comes before the operand as in (&(st=Moscrow)(cn=s*)), for queries, and then displays the results as shown below. This tool is free.
Microsoft Access
One of my favorite tools for working with databases or LDAP is Microsoft Access. Not enough people know about this powerful tool, which must be one reason Microsoft dropped it from Office. Now you have to buy it separately. But it is free with Office 365.
Access does two very powerful things.
First, it lets you make complex queries using a graphical interface. Then it writes SQL based on that for you, but you can ignore the complicated SQL. It lets you nest queries too. You would need to have some knowledge of programming to understand just how useful it is to be able to make a subset of data, to join that with another subset, and to create yet a third subset. This approach makes it possible to answer almost any question related to whatever data you have. But even the beginner can connect it to Active Directory, using ODBC, and play around with it to see how it works.
Second, like all Microsoft Office products, Access includes Visual Basic, which is one of the world’s easiest and oldest programming languages (Basic was by written Bill Gates and a few others). So you can write custom logic to update fields, to make queries, or to do even more complex tasks.
Zohno Z-Hire and Z-Term
These two tools used together let you create templates to speed up and standardize user creation. You could say it is a mini IDM (identity management) system where AD is the ‘system of record’. This means AD is the one system that contains all the fields and group memberships that show what other systems the user account has accounts in, and what permissions go with these accounts. Given that information, these tools can create accounts in Exchange, Microsoft Lynx, Office 364, and SalesForce.
Dell GPOADmin
Dell sells lots of different tools for Activity Directory. Most of them, like GPOADmin, are very inexpensive. This one costs $19 USD. What GPOADmn does is to more easily manage group policy objects. For example, you can delete older versions of the object incremental changes to reduce the size of the backup. There are extensive workflow approval tools to help you comply with the requirements to document all changes to user and group permissions. You can also schedule different tasks and run them in batch mode.
Microsoft AD Replication Status Tool
Replication is a key issue with any distributed LDAP system. If there are replication issues in a round-robin environment, then a newly-created user might not be able to log in right after they have created their account. This is because the authentication mechanism has consulted a different AD server than the one in which the user account was created, such that there is a replication delay or error.
The Microsoft ADREPLSTATUS tool checks the status of AD replication. It shows replication errors in a domain or forest. Then it allows you to prioritize errors and export them to a CSV file for analysis, or to import to a destination domain.
AD Audit Plus
ManageEngine tools are free or you can purchase them for support. ADAudit Plus tracks login activity plus changes to GPOs. So it provides the information that you need for compliance reporting. Also you could program it to flag when a user has been granted elevated privileges: this is a good indication of a hacker attack if this change was not made via the normal users or process.
SekChek Security Auditing
The importance of auditing depends on the country you are located in and the industry. The most regulated businesses are those in the financial services sector in the USA and UK. Most other businesses in the USA also have to comply with SOX and HIPAA regulations. European companies have their own set of regulations to follow. All of these require that you have an audit plan in place. Your auditor will expect you to have the tools to comply with the requirements of the plan.
SekChek is a tool that can help with this. SekChek’s AD security evaluation reports compare your AD installation security settings to industry standards to provide a rating ‘against industry average and leading security practices’.
NOTE: You should know that to comply with international auditing standards you will need yet another tool in addition to this, such as AD Audit Plus, as well as something like email or SharePoint to store proof of certification. Certification means documenting who gave permission to create each user account. There should be a workflow object or email that shows who gave access to each account. More complicated IDM systems do this, but you can design your own, using a combination of different tools including this one, as a more straightforward way to meet the requirement.
Windows Power Shell
Power Shell is for power users who don’t want to use graphical tools in all cases. Those who are comfortable with scripting languages will find the Power Shell built into Windows a good way to automate tasks. Power Shell is based on cmdlets, which are analogous to Python import modules. In other word it is a set of tools that are included at runtime.
The AD cmdlet presents a comfortable and natural way to look at the AD directory tree by presenting it as a hierarchical file system. So you can use cd and dir to navigate the database. When you load the cmdlet, a drive AD: is mounted. Then you cd ad: to change over to that part of the directory.
Leave a Comment